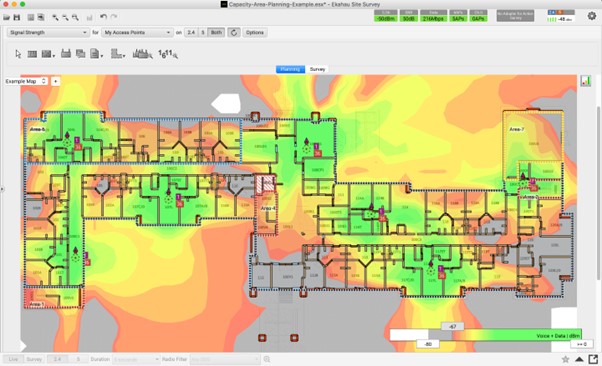
In the wake of COVID-19, the surge in remote working has profoundly impacted wireless networking when staff return to the office with Laptops.
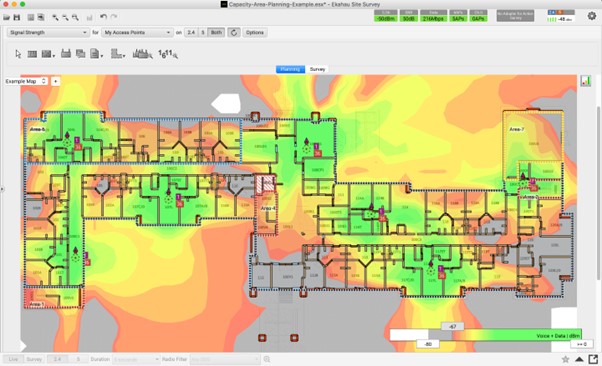
In the wake of COVID-19, the surge in remote working has profoundly impacted wireless networking when staff return to the office with Laptops.